Refresh 156-315.80 Free Draindumps For Check Point Certified Security Expert - R80 Certification
Act now and download your Check-Point 156-315.80 test today! Do not waste time for the worthless Check-Point 156-315.80 tutorials. Download Avant-garde Check-Point Check Point Certified Security Expert - R80 exam with real questions and answers and begin to learn Check-Point 156-315.80 with a classic professional.
Check 156-315.80 free dumps before getting the full version:
NEW QUESTION 1
What is a feature that enables VPN connections to successfully maintain a private and secure VPN session without employing Stateful Inspection?
- A. Stateful Mode
- B. VPN Routing Mode
- C. Wire Mode
- D. Stateless Mode
Answer: C
Explanation:
Wire Mode is a VPN-1 NGX feature that enables VPN connections to successfully fail over, bypassing Security Gateway enforcement. This improves performance and reduces downtime. Based on a trusted source and destination, Wire Mode uses internal interfaces and VPN Communities to maintain a private and secure VPN session, without employing Stateful Inspection. Since Stateful Inspection no longer takes place, dynamic-routing protocols that do not survive state verification in non-Wire Mode configurations can now be deployed. The VPN connection is no different from any other connections along a dedicated wire, thus the meaning of "Wire Mode".
NEW QUESTION 2
To enable Dynamic Dispatch on Security Gateway without the Firewall Priority Queues, run the following command in Expert mode and reboot:
- A. fw ctl Dyn_Dispatch on
- B. fw ctl Dyn_Dispatch enable
- C. fw ctl multik set_mode 4
- D. fw ctl multik set_mode 1
Answer: C
NEW QUESTION 3
Which firewall daemon is responsible for the FW CLI commands?
- A. fwd
- B. fwm
- C. cpm
- D. cpd
Answer: A
NEW QUESTION 4
What are the methods of SandBlast Threat Emulation deployment?
- A. Cloud, Appliance and Private
- B. Cloud, Appliance and Hybrid
- C. Cloud, Smart-1 and Hybrid
- D. Cloud, OpenServer and Vmware
Answer: A
NEW QUESTION 5
What has to be taken into consideration when configuring Management HA?
- A. The Database revisions will not be synchronized between the management servers
- B. SmartConsole must be closed prior to synchronized changes in the objects database
- C. If you wanted to use Full Connectivity Upgrade, you must change the Implied Rules to allow FW1_cpredundant to pass before the Firewall Control Connections.
- D. For Management Server synchronization, only External Virtual Switches are supporte
- E. So, if you wanted to employ Virtual Routers instead, you have to reconsider your design.
Answer: A
NEW QUESTION 6
SmartConsole R80 requires the following ports to be open for SmartEvent R80 management:
- A. 19090,22
- B. 19190,22
- C. 18190,80
- D. 19009,443
Answer: D
NEW QUESTION 7
Fill in the blank: Permanent VPN tunnels can be set on all tunnels in the community, on all tunnels for specific gateways, or ________.
- A. On all satellite gateway to satellite gateway tunnels
- B. On specific tunnels for specific gateways
- C. On specific tunnels in the community
- D. On specific satellite gateway to central gateway tunnels
Answer: C
NEW QUESTION 8
Which one of the following is true about Threat Emulation?
- A. Takes less than a second to complete
- B. Works on MS Office and PDF files only
- C. Always delivers a file
- D. Takes minutes to complete (less than 3 minutes)
Answer: D
NEW QUESTION 9
What does the Log "Views" tab show when SmartEvent is Correlating events?
- A. A list of common reports
- B. Reports for customization
- C. Top events with charts and graphs
- D. Details of a selected logs
Answer: C
NEW QUESTION 10
Where you can see and search records of action done by R80 SmartConsole administrators?
- A. In SmartView Tracker, open active log
- B. In the Logs & Monitor view, select “Open Audit Log View”
- C. In SmartAuditLog View
- D. In Smartlog, all logs
Answer: B
NEW QUESTION 11
During the Check Point Stateful Inspection Process, for packets that do not pass Firewall Kernel Inspection and are rejected by the rule definition, packets are:
- A. Dropped without sending a negative acknowledgment
- B. Dropped without logs and without sending a negative acknowledgment
- C. Dropped with negative acknowledgment
- D. Dropped with logs and without sending a negative acknowledgment
Answer: D
NEW QUESTION 12
What processes does CPM control?
- A. Object-Store, Database changes, CPM Process and web-services
- B. web-services, CPMI process, DLEserver, CPM process
- C. DLEServer, Object-Store, CP Process and database changes
- D. web_services, dle_server and object_Store
Answer: D
NEW QUESTION 13
How many users can have read/write access in Gaia at one time?
- A. Infinite
- B. One
- C. Three
- D. Two
Answer: B
NEW QUESTION 14
How often does Threat Emulation download packages by default?
- A. Once a week
- B. Once an hour
- C. Twice per day
- D. Once per day
Answer: D
NEW QUESTION 15
Which remote Access Solution is clientless?
- A. Checkpoint Mobile
- B. Endpoint Security Suite
- C. SecuRemote
- D. Mobile Access Portal
Answer: D
NEW QUESTION 16
Which of the following is NOT a type of Check Point API available in R80.10?
- A. Identity Awareness Web Services
- B. OPSEC SDK
- C. Mobile Access
- D. Management
Answer: C
NEW QUESTION 17
Fill in the blank: The tool _______ generates a R80 Security Gateway configuration report.
- A. infoCP
- B. infoview
- C. cpinfo
- D. fw cpinfo
Answer: C
NEW QUESTION 18
The Firewall Administrator is required to create 100 new host objects with different IP addresses. What API command can he use in the script to achieve the requirement?
- A. add host name <New HostName> ip-address <ip address>
- B. add hostname <New HostName> ip-address <ip address>
- C. set host name <New HostName> ip-address <ip address>
- D. set hostname <New HostName> ip-address <ip address>
Answer: A
NEW QUESTION 19
How many interfaces can you configure to use the Multi-Queue feature?
- A. 10 interfaces
- B. 3 interfaces
- C. 4 interfaces
- D. 5 interfaces
Answer: D
Explanation:
Note - References:
NEW QUESTION 20
Check Point recommends configuring Disk Space Management parameters to delete old log entries when available disk space is less than or equal to?
- A. 50%
- B. 75%
- C. 80%
- D. 15%
Answer: D
NEW QUESTION 21
View the rule below. What does the lock-symbol in the left column mean? (Choose the BEST answer.)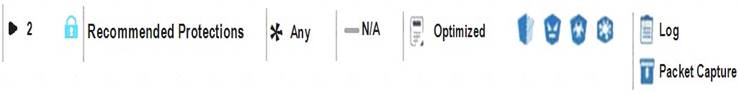
- A. The current administrator has read-only permissions to Threat Prevention Policy.
- B. Another user has locked the rule for editing.
- C. Configuration lock is presen
- D. Click the lock symbol to gain read-write access.
- E. The current administrator is logged in as read-only because someone else is editing the policy.
Answer: B
Explanation:
https://sc1.checkpoint.com/documents/R80/CP_R80_SecMGMT/html_frameset.htm?topic=documents/R80/CP_
NEW QUESTION 22
The Event List within the Event tab contains:
- A. a list of options available for running a query.
- B. the top events, destinations, sources, and users of the query results, either as a chart or in a tallied list.
- C. events generated by a query.
- D. the details of a selected event.
Answer: C
NEW QUESTION 23
What is the responsibility of SOLR process on R80.10 management server?
- A. Validating all data before it’s written into the database
- B. It generates indexes of data written to the database
- C. Communication between SmartConsole applications and the Security Management Server
- D. Writing all information into the database
Answer: B
NEW QUESTION 24
Check Point APIs allow system engineers and developers to make changes to their organization’s security policy with CLI tools and Web Services for all the following except:
- A. Create new dashboards to manage 3rd party task
- B. Create products that use and enhance 3rd party solutions
- C. Execute automated scripts to perform common tasks
- D. Create products that use and enhance the Check Point Solution
Answer: A
Explanation:
Check Point APIs let system administrators and developers make changes to the security policy with CLI tools and web-services. You can use an API to:
• Use an automated script to perform common tasks
• Integrate Check Point products with 3rd party solutions
• Create products that use and enhance the Check Point solution References:
NEW QUESTION 25
Fill in the blank: A _______ VPN deployment is used to provide remote users with secure access to internal corporate resources by authenticating the user through an internet browser.
- A. Clientless remote access
- B. Clientless direct access
- C. Client-based remote access
- D. Direct access
Answer: A
NEW QUESTION 26
You plan to automate creating new objects using new R80 Management API. You decide to use GAIA CLI for this task.
What is the first step to run management API commands on GAIA’s shell?
- A. mgmt_admin@teabag > id.txt
- B. mgmt_login
- C. login user admin password teabag
- D. mgmt_cli login user “admin” password “teabag” > id.txt
Answer: B
NEW QUESTION 27
Which command can you use to verify the number of active concurrent connections?
- A. fw conn all
- B. fw ctl pstat
- C. show all connections
- D. show connections
Answer: B
NEW QUESTION 28
......
Thanks for reading the newest 156-315.80 exam dumps! We recommend you to try the PREMIUM Certleader 156-315.80 dumps in VCE and PDF here: https://www.certleader.com/156-315.80-dumps.html (285 Q&As Dumps)