Top Tips Of Latest SY0-601 Free Exam Questions
Cause all that matters here is passing the CompTIA SY0-601 exam. Cause all that you need is a high score of SY0-601 CompTIA Security+ Exam exam. The only one thing you need to do is downloading Exambible SY0-601 exam study guides now. We will not let you down with our money-back guarantee.
Also have SY0-601 free dumps questions for you:
NEW QUESTION 1
A cybersecurity department purchased o new PAM solution. The team is planning to randomize the service account credentials of the Windows server first. Which of the following would be the BEST method to increase the security on the Linux server?
- A. Randomize the shared credentials
- B. Use only guest accounts to connect.
- C. Use SSH keys and remove generic passwords
- D. Remove all user accounts.
Answer: C
NEW QUESTION 2
A Chief Security Officer (CSO) is concerned about the amount of PII that is stored locally on each salesperson’s laptop. The sales department has a higher-than-average rate of lost equipment. Which of the following recommendations would BEST address the CSO’s concern?
- A. Deploy an MDM solution.
- B. Implement managed FDE.
- C. Replace all hard drives with SEDs.
- D. Install DLP agents on each laptop.
Answer: B
NEW QUESTION 3
The manager who is responsible for a data set has asked a security engineer to apply encryption to the data on a hard disk. The security engineer is an example of a:
- A. data controller.
- B. data owner
- C. data custodian.
- D. data processor
Answer: D
NEW QUESTION 4
A security auditor is reviewing vulnerability scan data provided by an internal security team. Which of the following BEST indicates that valid credentials were used?
- A. The scan results show open ports, protocols, and services exposed on the target host
- B. The scan enumerated software versions of installed programs
- C. The scan produced a list of vulnerabilities on the target host
- D. The scan identified expired SSL certificates
Answer: B
NEW QUESTION 5
A Chief Security Office's (CSO's) key priorities are to improve preparation, response, and recovery practices to minimize system downtime and enhance organizational resilience to ransomware attacks. Which of the following would BEST meet the CSO's objectives?
- A. Use email-filtering software and centralized account management, patch high-risk systems, and restrict administration privileges on fileshares.
- B. Purchase cyber insurance from a reputable provider to reduce expenses during an incident.
- C. Invest in end-user awareness training to change the long-term culture and behavior of staff and executives, reducing the organization's susceptibility to phishing attacks.
- D. Implement application whitelisting and centralized event-log management, and perform regular testing and validation of full backups.
Answer: D
NEW QUESTION 6
A company recently experienced a data breach and the source was determined to be an executive who was charging a phone in a public area. Which of the following would MOST likely have prevented this breach?
- A. A firewall
- B. A device pin
- C. A USB data blocker
- D. Biometrics
Answer: C
NEW QUESTION 7
A security administrator needs to create a RAIS configuration that is focused on high read speeds and fault tolerance. It is unlikely that multiple drivers will fail simultaneously. Which of the following RAID configurations should the administration use?
- A. RA1D 0
- B. RAID1
- C. RAID 5
- D. RAID 10
Answer: C
NEW QUESTION 8
A cybersecurity analyst reviews the log files from a web server and sees a series of files that indicates a directory-traversal attack has occurred. Which of the following is the analyst MOST likely seeing?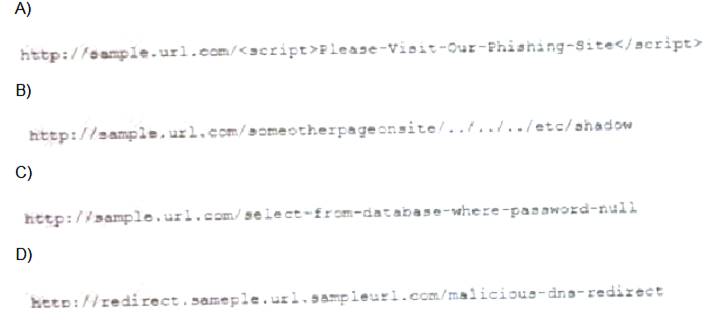
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: B
NEW QUESTION 9
An auditor is performing an assessment of a security appliance with an embedded OS that was vulnerable during the last two assessments. Which of the following BEST explains the appliance’s vulnerable state?
- A. The system was configured with weak default security settings.
- B. The device uses weak encryption ciphers.
- C. The vendor has not supplied a patch for the appliance.
- D. The appliance requires administrative credentials for the assessment.
Answer: C
NEW QUESTION 10
A user recent an SMS on a mobile phone that asked for bank delays. Which of the following social-engineering techniques was used in this case?
- A. SPIM
- B. Vishing
- C. Spear phishing
- D. Smishing
Answer: D
NEW QUESTION 11
Which of the following job roles would sponsor data quality and data entry initiatives that ensure business and regulatory requirements are met?
- A. The data owner
- B. The data processor
- C. The data steward
- D. The data privacy officer.
Answer: C
NEW QUESTION 12
Users have been issued smart cards that provide physical access to a building. The cards also contain tokens that can be used to access information systems. Users can log m to any thin client located throughout the building and see the same desktop each time. Which of the following technologies are being utilized to provide these capabilities? (Select TWO)
- A. COPE
- B. VDI
- C. GPS
- D. TOTP
- E. RFID
- F. BYOD
Answer: BE
NEW QUESTION 13
Which of the following disaster recovery tests is The LEAST time-consuming for the disaster recovery team?
- A. Tabletop
- B. Parallel
- C. Full interruption
- D. Simulation
Answer: D
NEW QUESTION 14
Which of the following is MOST likely to outline the roles and responsibilities of data controllers and data processors?
- A. SSAE SOC 2
- B. PCI DSS
- C. GDPR
- D. ISO 31000
Answer: C
NEW QUESTION 15
A security analyst needs to complete an assessment. The analyst is logged into a server and must use native tools to map services running on it to the server's listening ports. Which of the following tools can BEST accomplish this talk?
- A. Netcat
- B. Netstat
- C. Nmap
- D. Nessus
Answer: B
NEW QUESTION 16
A recently discovered zero-day exploit utilizes an unknown vulnerability in the SMB network protocol to rapidly infect computers. Once infected, computers are encrypted and held for ransom. Which of the following would BEST prevent this attack from reoccurring?
- A. Configure the perimeter firewall to deny inbound external connections to SMB ports.
- B. Ensure endpoint detection and response systems are alerting on suspicious SMB connections.
- C. Deny unauthenticated users access to shared network folders.
- D. Verify computers are set to install monthly operating system, updates automatically.
Answer: A
NEW QUESTION 17
A commercial cyber-threat intelligence organization observes IoCs across a variety of unrelated customers. Prior to releasing specific threat intelligence to other paid subscribers, the organization is MOST likely obligated by contracts to:
- A. perform attribution to specific APTs and nation-state actors.
- B. anonymize any PII that is observed within the IoC data.
- C. add metadata to track the utilization of threat intelligence reports.
- D. assist companies with impact assessments based on the observed data.
Answer: B
NEW QUESTION 18
Which of the following are requirements that must be configured for PCI DSS compliance? (Select TWO).
- A. Testing security systems and processes regularly
- B. Installing and maintaining a web proxy to protect cardholder data
- C. Assigning a unique ID to each person with computer access
- D. Encrypting transmission of cardholder data across private networks
- E. Benchmarking security awareness training for contractors
- F. Using vendor-supplied default passwords for system passwords
Answer: BD
NEW QUESTION 19
A company wants to deploy PKI on its Internet-facing website. The applications that are currently deployed are: www.company.com (main website)
www.company.com (main website) contactus.company.com (for locating a nearby location)
contactus.company.com (for locating a nearby location)  quotes.company.com (for requesting a price quote)
quotes.company.com (for requesting a price quote)
The company wants to purchase one SSL certificate that will work for all the existing applications and any future applications that follow the same naming conventions, such as store.company.com. Which of the following certificate types would BEST meet the requirements?
- A. SAN
- B. Wildcard
- C. Extended validation
- D. Self-signed
Answer: B
NEW QUESTION 20
A company is launching a new internet platform for its clients. The company does not want to implement its own authorization solution but instead wants to rely on the authorization provided by another platform. Which of the following is the BEST approach to implement the desired solution?
- A. OAuth
- B. TACACS+
- C. SAML
- D. RADIUS
Answer: D
NEW QUESTION 21
A retail executive recently accepted a job with a major competitor. The following week, a security analyst reviews the security logs and identifies successful logon attempts to access the departed executive's accounts. Which of the following security practices would have addressed the issue?
- A. A non-disclosure agreement
- B. Least privilege
- C. An acceptable use policy
- D. Ofboarding
Answer: D
NEW QUESTION 22
An end user reports a computer has been acting slower than normal for a few weeks. During an investigation, an analyst determines the system is sending the user's email address and a ten-digit number to an IP address once a day. The only recent log entry regarding the user's computer is the following: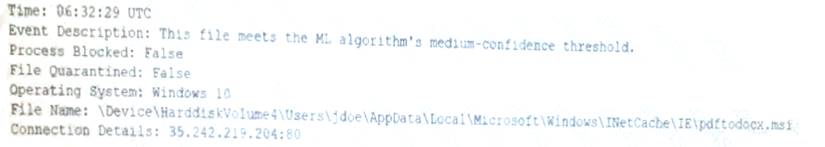
Which of the following is the MOST likely cause of the issue?
- A. The end user purchased and installed a PUP from a web browser
- B. A bot on the computer is brute forcing passwords against a website
- C. A hacker is attempting to exfiltrate sensitive data
- D. Ransomware is communicating with a command-and-control server.
Answer: A
NEW QUESTION 23
......
Recommend!! Get the Full SY0-601 dumps in VCE and PDF From Certshared, Welcome to Download: https://www.certshared.com/exam/SY0-601/ (New 218 Q&As Version)