The Secret Of CompTIA SY0-601 Test Preparation
Certleader offers free demo for SY0-601 exam. "CompTIA Security+ Exam", also known as SY0-601 exam, is a CompTIA Certification. This set of posts, Passing the CompTIA SY0-601 exam, will help you answer those questions. The SY0-601 Questions & Answers covers all the knowledge points of the real exam. 100% real CompTIA SY0-601 exams and revised by experts!
Free SY0-601 Demo Online For CompTIA Certifitcation:
NEW QUESTION 1
A company is adopting a BYOD policy and is looking for a comprehensive solution to protect company information on user devices. Which of the following solutions would BEST support the policy?
- A. Mobile device management
- B. Full-device encryption
- C. Remote wipe
- D. Biometrics
Answer: A
NEW QUESTION 2
A user enters a password to log in to a workstation and is then prompted to enter an authentication code. Which of the following MFA factors or attributes are being utilized in the authentication process? (Select TWO).
- A. Something you know
- B. Something you have
- C. Somewhere you are
- D. Someone you are
- E. Something you are
- F. Something you can do
Answer: BE
NEW QUESTION 3
A cybersecurity analyst needs to implement secure authentication to third-party websites without users’ passwords. Which of the following would be the BEST way to achieve this objective?
- A. OAuth
- B. SSO
- C. SAML
- D. PAP
Answer: C
NEW QUESTION 4
Which of the following BEST explains the reason why a server administrator would place a document named password.txt on the desktop of an administrator account on a server?
- A. The document is a honeyfile and is meant to attract the attention of a cyberintruder.
- B. The document is a backup file if the system needs to be recovered.
- C. The document is a standard file that the OS needs to verify the login credentials.
- D. The document is a keylogger that stores all keystrokes should the account be compromised.
Answer: A
NEW QUESTION 5
To secure an application after a large data breach, an e-commerce site will be resetting all users’ credentials. Which of the following will BEST ensure the site’s users are not compromised after the reset?
- A. A password reuse policy
- B. Account lockout after three failed attempts
- C. Encrypted credentials in transit
- D. A geofencing policy based on login history
Answer: C
NEW QUESTION 6
An analyst visits an internet forum looking for information about a tool. The analyst finds a threat that appears to contain relevant information. One of the posts says the following: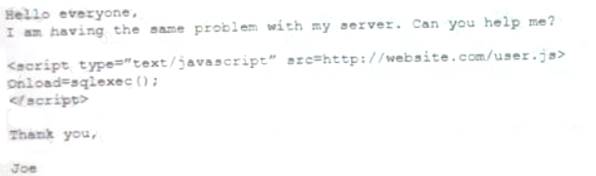
Which of the following BEST describes the attack that was attempted against the forum readers?
- A. SOU attack
- B. DLL attack
- C. XSS attack
- D. API attack
Answer: C
NEW QUESTION 7
An organization needs to implement more stringent controls over administrator/root credentials and service accounts. Requirements for the project include: Check-in/checkout of credentials
Check-in/checkout of credentials The ability to use but not know the password
The ability to use but not know the password  Automated password changes
Automated password changes Logging of access to credentials
Logging of access to credentials
Which of the following solutions would meet the requirements?
- A. OAuth 2.0
- B. Secure Enclave
- C. A privileged access management system
- D. An OpenID Connect authentication system
Answer: D
NEW QUESTION 8
The IT department at a university is concerned about professors placing servers on the university network in an attempt to bypass security controls. Which of the following BEST represents this type of threat?
- A. A script kiddie
- B. Shadow IT
- C. Hacktivism
- D. White-hat
Answer: B
NEW QUESTION 9
A cybersecurity administrator has a reduced team and needs to operate an on-premises network and security infrastructure efficiently. To help with the situation, the administrator decides to hire a service provider. Which of the following should the administrator use?
- A. SDP
- B. AAA
- C. IaaS
- D. MSSP
- E. Microservices
Answer: D
NEW QUESTION 10
A company recently set up an e-commerce portal to sell its product online. The company wants to start accepting credit cards for payment, which requires compliance with a security standard. Which of the following standards must the company comply with before accepting credit cards on its e-commerce platform?
- A. PCI DSS
- B. ISO 22301
- C. ISO 27001
- D. NIST CSF
Answer: A
NEW QUESTION 11
A Chief Executive Officer's (CEO) personal information was stolen in a social engineering attack. Which of the following sources would reveal if the CEO's personal information is for sale?
- A. Automated information sharing
- B. Open-source intelligence
- C. The dark web
- D. Vulnerability databases
Answer: C
NEW QUESTION 12
A user recently attended an exposition and received some digital promotional materials The user later noticed blue boxes popping up and disappearing on the computer, and reported receiving several spam emails, which the user did not open Which of the following is MOST likely the cause of the reported issue?
- A. There was a drive-by download of malware
- B. The user installed a cryptominer
- C. The OS was corrupted
- D. There was malicious code on the USB drive
Answer: D
NEW QUESTION 13
An organization has implemented a policy requiring the use of conductive metal lockboxes for personal electronic devices outside of a secure research lab. Which of the following did the organization determine to be the GREATEST risk to intellectual property when creating this policy?
- A. The theft of portable electronic devices
- B. Geotagging in the metadata of images
- C. Bluesnarfing of mobile devices
- D. Data exfiltration over a mobile hotspot
Answer: D
NEW QUESTION 14
A security analyst receives the configuration of a current VPN profile and notices the authentication is only applied to the IP datagram portion of the packet. Which of the following should the analyst implement to authenticate the entire packet?
- A. AH
- B. ESP
- C. SRTP
- D. LDAP
Answer: B
NEW QUESTION 15
A startup company is using multiple SaaS and IaaS platform to stand up a corporate infrastructure and build out a customer-facing web application. Which of the following solutions would be BEST to provide security, manageability, and visibility into the platforms?
- A. SIEM
- B. DLP
- C. CASB
- D. SWG
Answer: C
NEW QUESTION 16
A security analyst needs to produce a document that details how a security incident occurred, the steps that were taken for recovery, and how future incidents can be avoided. During which of the following stages of the response process will this activity take place?
- A. Recovery
- B. Identification
- C. Lessons learned
- D. Preparation
Answer: C
NEW QUESTION 17
A company is implementing MFA for all applications that store sensitive data. The IT manager wants MFA to be non-disruptive and user friendly. Which of the following technologies should the IT manager use when implementing MFA?
- A. One-time passwords
- B. Email tokens
- C. Push notifications
- D. Hardware authentication
Answer: C
NEW QUESTION 18
Which of the following will provide the BEST physical security countermeasures to stop intruders? (Select TWO.)
- A. Alarms
- B. Signage
- C. Lighting
- D. Mantraps
- E. Fencing
- F. Sensors
Answer: DE
NEW QUESTION 19
Which of the following would MOST likely support the integrity of a voting machine?
- A. Asymmetric encryption
- B. Blockchain
- C. Transport Layer Security
- D. Perfect forward secrecy
Answer: D
NEW QUESTION 20
Which of the following is the purpose of a risk register?
- A. To define the level or risk using probability and likelihood
- B. To register the risk with the required regulatory agencies
- C. To identify the risk, the risk owner, and the risk measures
- D. To formally log the type of risk mitigation strategy the organization is using
Answer: C
NEW QUESTION 21
Which of the following organizational policies are MOST likely to detect fraud that is being conducted by existing employees? (Select TWO).
- A. Offboarding
- B. Mandatory vacation
- C. Job rotation
- D. Background checks
- E. Separation of duties
- F. Acceptable use
Answer: BC
NEW QUESTION 22
A network administrator is setting up wireless access points in all the conference rooms and wants to authenticate device using PKI. Which of the following should the administrator configure?
- A. A captive portal
- B. PSK
- C. 802.1X
- D. WPS
Answer: C
NEW QUESTION 23
......
Recommend!! Get the Full SY0-601 dumps in VCE and PDF From 2passeasy, Welcome to Download: https://www.2passeasy.com/dumps/SY0-601/ (New 218 Q&As Version)