Top Tips Of Up To The Immediate Present N10-009 Test Question
It is impossible to pass CompTIA N10-009 exam without any help in the short term. Come to Ucertify soon and find the most advanced, correct and guaranteed CompTIA N10-009 practice questions. You will get a surprising result by our Abreast of the times CompTIA Network+ Exam practice guides.
Free demo questions for CompTIA N10-009 Exam Dumps Below:
NEW QUESTION 1
Which of the following protocols can be routed?
- A. FCoE
- B. Fibre Channel
- C. iSCSl
- D. NetBEUI
Answer: C
Explanation:
iSCSI (Internet Small Computer System Interface) is a protocol that allows SCSI commands to be transported over IP networks1. iSCSI can be routed because it contains a network address and a device address, as required by a routable protocol2. iSCSI can be used to access block-level storage devices over a network, such as SAN (Storage Area Network).
FCoE (Fibre Channel over Ethernet) is a protocol that allows Fibre Channel frames to be encapsulated and transported over Ethernet networks1. FCoE cannot be routed because it does not contain a network address, only a device address. FCoE operates at the data link layer and requires special switches and adapters to support it. FCoE can also be used to access block-level storage devices over a network, such as SAN.
Fibre Channel is a protocol that provides high-speed and low-latency communication between servers and storage devices1. Fibre Channel cannot be routed because it does not use IP networks, but rather its own dedicated network infrastructure. Fibre Channel operates at the physical layer and the data link layer and requires special cables, switches, and adapters to support it. Fibre Channel can also be used to access block-level storage devices over a network, such as SAN.
NetBEUI (NetBIOS Extended User Interface) is an old protocol that provides session-level communication between devices on a local network1. NetBEUI cannot be routed because it does not contain a network address, only a device address. NetBEUI operates at the transport layer and relies on NetBIOS for name resolution. NetBEUI is obsolete and has been replaced by other protocols, such as TCP/IP.
NEW QUESTION 2
The following configuration is applied to a DHCP server connected to a VPN concentrator: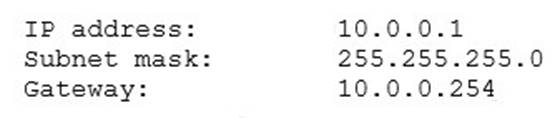
There are 300 non-concurrent sales representatives who log in for one hour a day to upload reports, and 252 of these representatives are able to connect to the VPN without any Issues. The remaining sales representatives cannot connect to the VPN over the course of the day. Which of the following can be done to resolve the issue without utilizing additional resources?
- A. Decrease the lease duration
- B. Reboot the DHCP server
- C. Install a new VPN concentrator
- D. Configure a new router
Answer: A
Explanation:
Decreasing the lease duration on the DHCP server will cause clients to renew their IP address leases more frequently, freeing up IP addresses for other clients to use. References: CompTIA Network+ Certification Study Guide, Chapter 3: IP Addressing.
NEW QUESTION 3
A company is designing a new complex. The primary and alternate data centers will be in separate buildings 6.2mi (10km) apart and will be connected via fiber.
Which of the following types of SFP is the best choice?
- A. 10GBASE-SR
- B. 10000BASE-LX
- C. 10GBASE-LR
- D. 1000BASE-SX
Answer: C
Explanation:
10GBASE-LR is the best choice for connecting two data centers that are 6.2 miles (10 km) apart via fiber, because it supports a maximum distance of 6.2 miles (10 km) over single- mode fiber. 10GBASE-SR and 1000BASE-SX are designed for short-range connections over multi-mode fiber, and they can only reach up to 1,312 feet (400 m) and 1,804 feet (550 m), respectively. 10000BASE-LX is a typo and does not exist as a standard. References:
✑ Network Transceivers – CompTIA Network+ N10-007 – 2.11
✑ CompTIA Network+ Certification Exam Objectives2
NEW QUESTION 4
A switch is connected to another switch. Incompatible hardware causes a surge in traffic on both switches. Which of the following configurations will cause traffic to pause, allowing the switches to drain buffers?
- A. Speed
- B. Flow control
- C. 802.1Q
- D. Duplex
Answer: B
Explanation:
Flow control is a mechanism that allows a network device to regulate the amount of traffic it can receive or send. Flow control can help prevent congestion and buffer overflow by sending pause frames or signals to the sender when the receiver’s buffer is full or nearly full. Flow control can cause traffic to pause, allowing the switches to drain buffers and resume normal operation. Speed is a parameter that determines the data transfer rate of a network link. 802.1Q is a standard for VLAN (Virtual Local Area Network) tagging, which allows multiple logical networks to share the same physical infrastructure. Duplex is a mode of communication that determines how data is transmitted and received on a link. Full duplex allows simultaneous transmission and reception, while half duplex allows only one direction at a time.
References: CompTIA Network+ Certification Exam Objectives Version 7.0 (N10-007), Objective 1.5: Compare and contrast network cabling types, standards and speeds.
NEW QUESTION 5
A lab environment hosts Internet-facing web servers and other experimental machines, which technicians use for various tasks A technician installs software on one of the web servers to allow communication to the company's file server, but it is unable to connect to it Other machines in the building are able to retrieve files from the file server. Which of the following is the MOST likely reason the web server cannot retrieve the files, and what should be done to resolve the problem?
- A. The lab environment's IDS is blocking the network traffic 1 he technician can whitelist the new application in the IDS
- B. The lab environment is located in the DM2, and traffic to the LAN zone is denied by defaul
- C. The technician can move the computer to another zone or request an exception from the administrator.
- D. The lab environment has lost connectivity to the company router, and the switch needs to be reboote
- E. The technician can get the key to the wiring closet and manually restart the switch
- F. The lab environment is currently set up with hubs instead of switches, and the requests are getting bounced back The technician can submit a request for upgraded equipment to management.
Answer: B
Explanation:
The lab environment is located in the DMZ, and traffic to the LAN zone is denied by default. This is the most likely reason why the web server cannot retrieve files from the file server, and the technician can either move the computer to another zone or request an exception from the administrator to resolve the problem. A DMZ (Demilitarized Zone) is a network segment that separates the internal network (LAN) from the external network (Internet). It usually hosts public-facing servers such as web servers, email servers, or FTP servers that need to be accessed by both internal and external users. A firewall is used to control the traffic between the DMZ and the LAN zones, and usually denies traffic from the DMZ to the LAN by default for security reasons. Therefore, if a web server in the DMZ needs to communicate with a file server in the LAN, it would need a special rule or permission from the firewall administrator. References: https://www.cisco.com/c/en/us/support/docs/ip/access-lists/13608-21.html
NEW QUESTION 6
Which of the following network topologies involves sending all traffic through a single point?
- A. Mesh
- B. Hybrid
- C. Hub-and-spoke
- D. Point-to-point
Answer: C
Explanation:
Hub-and-spoke is a network topology where each node connects to a central switching device, such as a hub or a switch. All traffic between the nodes must pass through the central device, which acts as a single point of communication and control. Hub-and-spoke topology is simple, easy to manage, and cost-effective, but it also has drawbacks, such as low redundancy, high latency, and scalability issues.
References:
✑ Network Topologies – N10-008 CompTIA Network+ : 1.21
✑ CompTIA Network+ Certification Exam Objectives, page 92
NEW QUESTION 7
While using a secure conference call connection over a corporate VPN, a user moves from a cellular connection to a hotel wireless network. Although the wireless connection and the VPN show a connected status, no network connectivity is present. Which of the following is the most likely cause of this issue?
- A. MAC filtering is configured on the wireless connection.
- B. The VPN and the WLAN connection have an encryption protocol mismatch.
- C. The WLAN is using a captive portal that requires further authentication.
- D. Wireless client isolation is enforced on the WLAN settings.
Answer: C
Explanation:
A captive portal is a web page that is displayed to newly connected users of a Wi-Fi network before they are granted broader access to network resources. Captive portals are commonly used to present a landing or log-in page which may require authentication, payment, acceptance of an end-user license agreement, acceptable use policy, survey completion, or other valid credentials that both the host and user agree to adhere by123
A possible cause of the issue is that the user has not completed the captive portal authentication process, which prevents the VPN from establishing a secure connection over the Wi-Fi network. The user may need to open a web browser and follow the instructions on the captive portal page to gain full access to the internet.
NEW QUESTION 8
A technician is expanding a wireless network and adding new access points. The company requires that each access point broadcast the same SSID. Which of the following should the technician implement for this requirement?
- A. MIMO
- B. Roaming
- C. Channel bonding
- D. Extended service set
Answer: D
Explanation:
An extended service set (ESS) is a wireless network that consists of two or more access points (APs) that share the same SSID and are connected by a distribution system, such as a switch or a router. An ESS allows wireless clients to roam seamlessly between different APs without losing connectivity or changing network settings. An ESS can also increase the coverage area and capacity of a wireless network
NEW QUESTION 9
Which of the following will reduce routing table lookups by performing packet forwarding decisions independently of the network layer header?
- A. MPLS
- B. mGRE
- C. EIGRP
- D. VRRP
Answer: A
Explanation:
Multiprotocol Label Switching, or MPLS, is a networking technology that routes traffic using the shortest path based on “labels,” rather than network addresses, to handle forwarding over private wide area networks. As a scalable and protocol- independent solution, MPLS assigns labels to each data packet, controlling the path the packet follows. MPLS greatly improves the speed of traffic, so users don’t experience downtime when connected to the network.
NEW QUESTION 10
An administrator is investigating reports of network slowness in a building. While looking at the uplink interface statistics In the switch's CLI, the administrator discovers the uplink Is at 100% utilization However, the administrator is unsure how to Identify what traffic is causing the saturation. Which of the following tools should the administrator utilize to identify the source and destination addresses of the traffic?
- A. SNMP
- B. Traps
- C. Syslog
- D. NetFlow
Answer: D
Explanation:
To identify the source and destination addresses of the traffic causing network saturation, the network administrator should use a network protocol analyzer that supports the NetFlow protocol. NetFlow is a network protocol that collects IP traffic information as it enters or exits an interface and sends it to a NetFlow collector for analysis. This data includes the source and destination addresses of the traffic, the ports used, and the number of bytes and packets transferred.
Therefore, the correct answer is option D, NetFlow.
Reference: CompTIA Network+ Study Guide, Exam N10-007, Fourth Edition, by Todd Lammle (Chapter 6: Network Devices)
NEW QUESTION 11
A bank installed a new smart TV to stream online video services, but the smart TV was not able to connect to the branch Wi-Fi. The next day. a technician was able to connect the TV to the Wi-Fi, but a bank laptop lost network access at the same time. Which of the following is the MOST likely cause?
- A. DHCP scope exhaustion
- B. AP configuration reset
- C. Hidden SSID
- D. Channel overlap
Answer: A
Explanation:
DHCP scope exhaustion is the situation when a DHCP server runs out of available IP addresses to assign to clients. DHCP stands for Dynamic Host Configuration Protocol, which is a network protocol that automatically assigns IP addresses and other configuration parameters to clients on a network. A DHCP scope is a range of IP addresses that a DHCP server can distribute to clients. If the DHCP scope is exhausted, new clients will not be able to obtain an IP address and connect to the network. This can explain why the smart TV was not able to connect to the branch Wi-Fi on the first day, and why the bank laptop lost network access on the next day when the TV was connected. The technician should either increase the size of the DHCP scope or reduce the lease time of the IP addresses to avoid DHCP scope exhaustion. References: [CompTIA Network+ Certification Exam Objectives], DHCP Scope Exhaustion - What Is It? How Do You Fix It?
NEW QUESTION 12
Which of the following connector types would be used to connect to the demarcation point and provide network access to a cable modem?
- A. F-type
- B. RJ45
- C. LC
- D. RJ11
Answer: A
Explanation:
An F-type connector is a type of coaxial connector that is commonly used to connect a cable modem to the demarcation point, which is the point at which the cable provider's network ends and the customer's network begins. The F-type connector is a threaded connector that is typically used for television, cable modem, and satellite antenna connections.
NEW QUESTION 13
A network team is getting reports that air conditioning is out in an IDF. The team would like to determine whether additional network issues are occurring. Which of the following should the network team do?
- A. Confirm that memory usage on the network devices in the IDF is normal.
- B. Access network baseline data for references to an air conditioning issue.
- C. Verify severity levels on the corporate syslog server.
- D. Check for SNMP traps from a network device in the IDF.
- E. Review interface statistics looking for cyclic redundancy errors.
Answer: D
Explanation:
"Baselines play an integral part in network documentation because they let you monitor the network’s overall performance. In simple terms, a baseline is a measure of performance that indicates how hard the network is working and where network resources are spent. The purpose of a baseline is to provide a basis of comparison. For example, you can compare the network’s performance results taken in March to results taken in June, or from one year to the next. More commonly, you would compare the baseline information at a time when the network is having a problem to information recorded when the network was operating with greater efficiency. Such comparisons help you determine whether there has been a problem with the network, how significant that problem is, and even where the problem lies."
NEW QUESTION 14
A company's web server is hosted at a local ISP. This is an example of:
- A. allocation.
- B. an on-premises data center.
- C. a branch office.
- D. a cloud provider.
Answer: D
NEW QUESTION 15
Classification using labels according to information sensitivity and impact in case of unauthorized access or leakage is a mandatory component of:
- A. an acceptable use policy.
- B. a memorandum of understanding.
- C. data loss prevention,
- D. a non-disclosure agreement.
Answer: C
Explanation:
Data loss prevention (DLP) is a set of tools and processes that aim to prevent unauthorized access or leakage of sensitive information. One of the components of DLP is data classification, which involves labeling data according to its information sensitivity and impact in case of unauthorized disclosure. Data classification helps to identify and protect the most critical and confidential data and apply appropriate security controls and policies. References: Network+ Study Guide Objective 5.1: Explain the importance of policies, processes and procedures for IT governance. Subobjective: Data loss prevention.
NEW QUESTION 16
Which of the following use cases would justify the deployment of an mGRE hub-and-spoke topology?
- A. An increase in network security using encryption and packet encapsulation
- B. A network expansion caused by an increase in the number of branch locations to the headquarters
- C. A mandatory requirement to increase the deployment of an SDWAN network
- D. An improvement in network efficiency by increasing the useful packet payload
Answer: B
Explanation:
mGRE (Multipoint GRE) is a type of GRE (Generic Routing Encapsulation) tunnel that allows a single interface to support multiple tunnel endpoints, instead of having to configure a separate point-to-point tunnel for each destination. mGRE simplifies the configuration and management of large-scale VPN networks, such as DMVPN (Dynamic Multipoint VPN), which is a Cisco technology that uses mGRE, NHRP (Next Hop Resolution Protocol), and IPsec to create secure and dynamic VPN connections between a hub and multiple spokes1.
A network expansion caused by an increase in the number of branch locations to the headquarters would justify the deployment of an mGRE hub-and-spoke topology, because it would reduce the complexity and overhead of configuring and maintaining multiple point- to-point tunnels between the hub and each spoke. mGRE would also enable spoke-to- spoke communication without having to go through the hub, which would improve the network performance and efficiency23.
The other options are not directly related to the use case of mGRE hub-and-spoke topology. An increase in network security using encryption and packet encapsulation can be achieved by using IPsec, which is a separate protocol that can be applied to any type of GRE tunnel, not just mGRE. A mandatory requirement to increase the deployment of an SDWAN network can be met by using various technologies and vendors, not necessarily mGRE or DMVPN. An improvement in network efficiency by increasing the useful packet payload can be achieved by using various techniques, such as compression, fragmentation, or QoS, not specifically mGRE.
ReferencesUnderstanding Cisco Dynamic Multipoint VPN - DMVPN, mGRE, NHRPMGRE Easy Steps - Cisco CommunityWhat is DMVPN (Dynamic Multipoint VPN), NHRP, mGRE and How to configu - Cisco Community
NEW QUESTION 17
A network technician is troubleshooting a connectivity issue. All users within the network report that they are unable to navigate to websites on the internet; however, they can still access local network resources. The technician issues a command and receives the following results: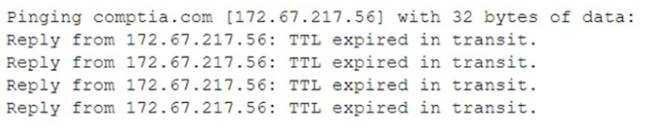
Which of the following best explains the result of this command?
- A. Incorrect VLAN settings
- B. Upstream routing loop
- C. Network collisions
- D. DNS misconfiguration
Answer: D
Explanation:
The users are unable to navigate to websites on the internet but can access local network resources, indicating a possible DNS issue. The ping command result showing “TTL expired in transit” suggests that packets are not reaching their destination due to a DNS misconfiguration that is not resolving website names into IP addresses correctly3. A possible solution is to check and correct the DNS server settings on the network devices4.
References: 3: What does “TTL expired in transit” mean?54: CompTIA Network+ N10-008 Cert Guide - Chapter 14: Network Monitoring2
NEW QUESTION 18
Which of the following protocol types describes secure communication on port 443?
- A. ICMP
- B. UDP
- C. TCP
- D. IP
Answer: C
Explanation:
TCP is the protocol type that describes secure communication on port 443. TCP (Transmission Control Protocol) is a connection-oriented protocol that provides reliable and ordered delivery of data packets over an IP network. TCP uses port numbers to identify different applications or services on a device. Port 443 is the default port for HTTPS (Hypertext Transfer Protocol Secure), which is an extension of HTTP that uses SSL (Secure Sockets Layer) or TLS (Transport Layer Security) encryption to protect data in transit between a web server and a web browser. References: https://www.cisco.com/c/en/us/support/docs/ip/routing-information-protocol-rip/13788- 3.html
NEW QUESTION 19
A customer reports there is no access to resources following the replacement of switches. A technician goes to the site to examine the configuration and discovers redundant links between two switches. Which of the following is the reason the network is not functional?
- A. The ARP cache has become corrupt.
- B. CSMA/CD protocols have failed.
- C. STP is not configured.
- D. The switches are incompatible models
Answer: C
Explanation:
The reason the network is not functional is that STP (Spanning Tree Protocol) is not configured on the switches. STP is a protocol that prevents loops in a network topology by blocking redundant links between switches. If STP is not enabled, the switches will forward broadcast frames endlessly, creating a broadcast storm that consumes network resources and disrupts communication. References: CompTIA Network+ N10-008 Certification Study Guide, page 67; The Official CompTIA Network+ Student Guide (Exam N10-008), page 2-14.
NEW QUESTION 20
A user tries to ping 192.168.1.100 from the command prompt on the 192.168.2.101 network but gets the following response: U.U.U.U. Which of the following needs to be configured for these networks to reach each other?
- A. Network address translation
- B. Default gateway
- C. Loopback
- D. Routing protocol
Answer: B
Explanation:
A default gateway is a device that routes traffic from one network to another network, such as the Internet. A default gateway is usually configured on each host device to specify the IP address of the router that connects the host’s network to other networks. In this case, the user’s device and the destination device are on different networks (192.168.1.0/24 and 192.168.2.0/24), so the user needs to configure a default gateway on their device to reach the destination device. References: https://partners.comptia.org/docs/default-source/resources/comptia-network-n10-008-exam-objectives-(2-0), https://www.techopedia.com/definition/25761/default-gateway
NEW QUESTION 21
......
Recommend!! Get the Full N10-009 dumps in VCE and PDF From Dumps-hub.com, Welcome to Download: https://www.dumps-hub.com/N10-009-dumps.html (New 179 Q&As Version)