What Tested N10-009 Testing Engine Is
Your success in CompTIA N10-009 is our sole target and we develop all our N10-009 braindumps in a way that facilitates the attainment of this target. Not only is our N10-009 study material the best you can find, it is also the most detailed and the most updated. N10-009 Practice Exams for CompTIA N10-009 are written to the highest standards of technical accuracy.
Also have N10-009 free dumps questions for you:
NEW QUESTION 1
An ISP is unable to provide services to a user in a remote area through cable and DSL. Which of the following is the NEXT best solution to provide services without adding external infrastructure?
- A. Fiber
- B. Leased line
- C. Satellite
- D. Metro optical
Answer: C
Explanation:
If an ISP is unable to provide services to a user in a remote area through cable and DSL, the next best solution to provide services without adding external infrastructure would likely be satellite. Satellite is a wireless communication technology that uses a network of satellites orbiting the Earth to transmit and receive data. It is well-suited for providing connectivity to remote or rural areas where other types of infrastructure may not be available or may be cost-prohibitive to install.
NEW QUESTION 2
After a company installed a new IPS, the network is experiencing speed degradation. A network administrator is troubleshooting the issue and runs a speed test. The results from the different network locations are as follows:
Which of the following is the most likely issue?
- A. Packet loss
- B. Bottlenecking
- C. Channel overlap
- D. Network congestion
Answer: B
Explanation:
The most likely issue is bottlenecking. Bottlenecking occurs when a component or device limits the performance or capacity of the network. In this case, the IPS (intrusion prevention system) may be causing a bottleneck by inspecting and filtering the incoming and outgoing traffic, which reduces the speed and bandwidth available for the network devices12
To confirm this issue, the network administrator can compare the speed test results before and after installing the IPS, and check the IPS configuration and logs for any errors or warnings. The network administrator can also try to bypass the IPS temporarily and run the speed test again to see if there is any improvement3
If the IPS is indeed the cause of the bottleneck, the network administrator can try to optimize the IPS settings, such as adjusting the inspection rules, thresholds, and priorities, to reduce the processing overhead and latency. Alternatively, the network administrator can upgrade the IPS hardware or software, or add more IPS devices to balance the load and increase the throughput45
1: What is Network Congestion? Common Causes and How to Fix Them? -
GeeksforGeeks 2: Network congestion - Wikipedia 3: How to Fix Packet Loss - Lifewire 4: How to Optimize Your IPS Performance - Cisco 5: How to Avoid Network Bottlenecks - TechRepublic
NEW QUESTION 3
A technician is assisting a user who cannot connect to a network resource. The technician first checks for a link light. According to troubleshooting methodology, this is an example of:
- A. using a bottom-to-top approach.
- B. establishing a plan of action.
- C. documenting a finding.
- D. questioning the obvious.
Answer: A
Explanation:
Using a bottom-to-top approach means starting from the physical layer and moving up the OSI model to troubleshoot a network problem. Checking for a link light is a physical layer check that verifies the connectivity of the network cable and device. References: https://www.professormesser.com/network-plus/n10-007/troubleshooting- methodologies-2/
NEW QUESTION 4
Which of the following is a security flaw in an application or network?
- A. A threat
- B. A vulnerability
- C. An exploit
- D. A risk
Answer: B
Explanation:
A vulnerability is a security flaw in an application or network that can be exploited by an attacker, allowing them to gain access to sensitive data or take control of the system. Vulnerabilities can range from weak authentication methods to unpatched software, allowing attackers to gain access to the system or data they would not otherwise be able to access. Exploits are programs or techniques used to take advantage of vulnerabilities, while threats are potential dangers, and risks are the likelihood of a threat becoming a reality.
NEW QUESTION 5
An organization wants to implement a method of centrally managing logins to network services. Which of the following protocols should the organization use to allow for authentication, authorization and auditing?
- A. MS-CHAP
- B. RADIUS
- C. LDAPS
- D. RSTP
Answer: B
Explanation:
RADIUS (Remote Authentication Dial-In User Service) is a protocol that should be used by the organization to allow for authentication, authorization, and auditing of network services. RADIUS is an AAA (Authentication, Authorization, and Accounting) protocol that manages network access by verifying user credentials, granting access permissions, and logging user activities. RADIUS uses a client-server model where a RADIUS client (such as a router, switch, or VPN server) sends user information to a RADIUS server (such as an authentication server) for verification and authorization. The RADIUS server can also send accounting information to another server for billing or reporting purposes. References: https://www.cisco.com/c/en/us/support/docs/security- vpn/remote-authentication-dial-user-service-radius/13838-10.html
NEW QUESTION 6
A network technician is troubleshooting an area where the wireless connection to devices is poor. The technician theorizes that the signal-to-noise ratio in the area is causing the issue. Which of the following should the technician do NEXT?
- A. Run diagnostics on the relevant devices.
- B. Move the access point to a different location.
- C. Escalate the issue to the vendor's support team.
- D. Remove any electronics that might be causing interference.
Answer: D
NEW QUESTION 7
A customer connects a firewall to an ISP router that translates traffic destined for the internet. The customer can connect to the internet but not to the remote site. Which of the following will verify the status of NAT?
- A. tcpdump
- B. nmap
- C. ipconfig
- D. tracert
Answer: A
Explanation:
tcpdump is a command-line tool that can capture and analyze network traffic on a given interface. tcpdump can verify the status of NAT by showing the source and destination IP addresses of the packets before and after they pass through the ISP router that translates traffic destined for the internet. tcpdump can also show the NAT protocol and port numbers used by the router. nmap, ipconfig, and tracert are not suitable tools for verifying the status of NAT, as they do not show the IP address translation process.
References
✑ 1: Network Address Translation – N10-008 CompTIA Network+ : 1.4
✑ 2: CompTIA Network+ N10-008 Certification Study Guide, page 95-96
✑ 3: CompTIA Network+ N10-008 Exam Subnetting Quiz, question 16
✑ 4: CompTIA Network+ N10-008 Certification Practice Test, question 7
NEW QUESTION 8
Users are unable to access files on their department share located on flle_server 2. The network administrator has been tasked with validating routing between networks hosting workstation A and file server 2.
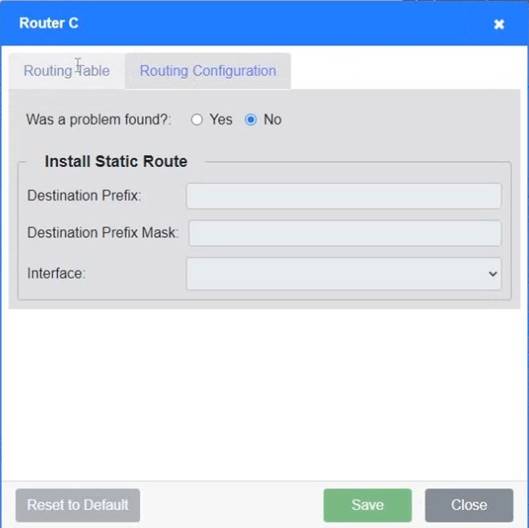
INSTRUCTIONS
Click on each router to review output, identity any Issues, and configure the appropriate solution
If at any time you would like to bring back the initial state of trie simulation, please click the reset All button;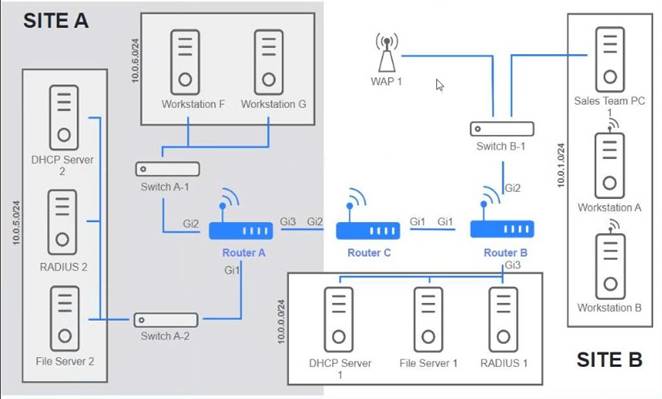
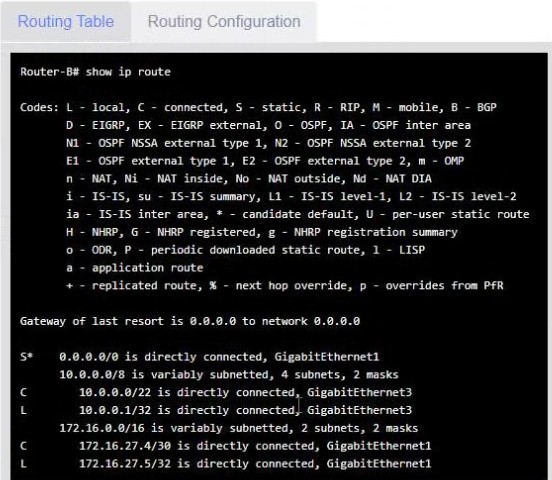
Solution:
See the solution configuration below in Explanation.
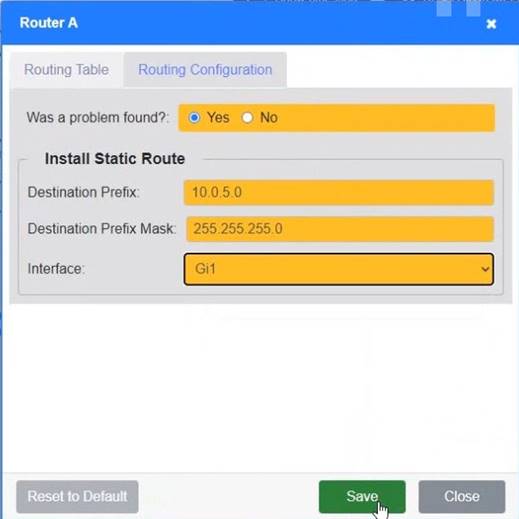
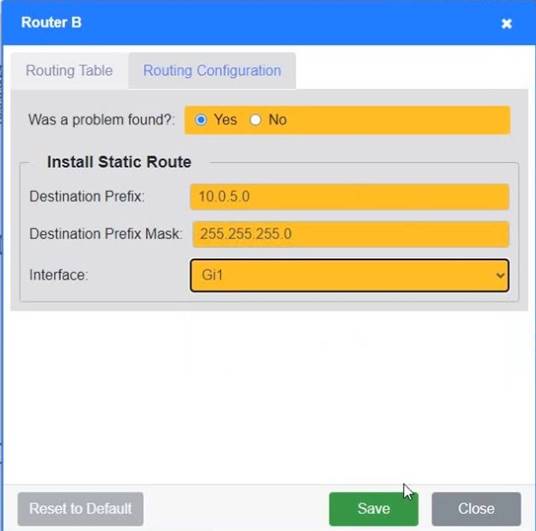
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 9
Which of the following can be used to identify users after an action has occurred?
- A. Access control vestibule
- B. Cameras
- C. Asset tag
- D. Motion detectors
Answer: B
Explanation:
Cameras can be used to identify users after an action has occurred by recording their faces, clothing, or other distinctive features. Cameras are often used as a deterrent and a forensic tool for security purposes. Access control vestibules, asset tags, and motion detectors are not effective in identifying users, but rather in controlling access, tracking assets, and detecting movement.
References:
CompTIA Network+ N10-008 Certification Exam Objectives, Domain 5.0: Network Security, Subobjective 5.1: Summarize the importance of physical security controls, page 231 CompTIA Network+ Certification All-in-One Exam Guide, Eighth Edition (Exam N10-008), Chapter 18: Network Security, Section: Physical Security, page 7372
NEW QUESTION 10
An ARP request is broadcasted and sends the following request. ''Who is 192.168.1.200?
Tell 192.168.1.55''
At which of the following layers of the OSI model does this request operate?
- A. Application
- B. Data link
- C. Transport
- D. Network
- E. Session
Answer: B
Explanation:
An ARP request operates at the data link layer of the OSI model. ARP (Address Resolution Protocol) is a protocol that maps IP addresses to MAC addresses on a local area network. It allows devices to communicate with each other without knowing their MAC addresses beforehand. ARP operates at the data link layer (layer 2) of the OSI model, which is responsible for framing and addressing data packets on a physical medium. References: https://www.cisco.com/c/en/us/support/docs/ip/routing-information- protocol-rip/13788-3.html
NEW QUESTION 11
An administrator would like to have two servers at different geographical locations provide fault tolerance and high performance while appearing as one URL to users. Which of the following should the administrator implement?
- A. Load balancing
- B. Multipathing
- C. NIC teaming
- D. Warm site
Answer: B
Explanation:
Load balancing is a technique that can be used to provide fault tolerance and high performance while appearing as one URL to users. It is achieved by distributing the workload across multiple servers, which are usually located in different geographical locations. This allows for high performance and fault tolerance, as if one server fails, the other will take its place. Additionally, the multiple servers appear as one URL to the users, eliminating the need for the users to switch between servers.
NEW QUESTION 12
A software developer changed positions within a company and is now a sales engineer. The security team discovered that the former software developer had been modifying code to implement small features requested by customers. Which of the following would be the best thing for the security administrator to implement to prevent this from happening?
- A. A software patching policy
- B. A role-based access control policy
- C. Firewalls on the software development servers
- D. Longer and more complex password requirements
Answer: B
Explanation:
A role-based access control (RBAC) policy is a security measure that assigns permissions and privileges to users based on their roles and responsibilities within an organization. RBAC helps to enforce the principle of least privilege, which states that users should only have the minimum level of access required to perform their tasks. RBAC also helps to prevent unauthorized access, modification, or misuse of sensitive data or resources by limiting the scope and impact of user actions.
A software patching policy, firewalls on the software development servers, and longer and more complex password requirements are all good security practices, but they do not directly address the issue of preventing the former software developer from modifying code. A software patching policy ensures that software is updated regularly to fix bugs and vulnerabilities, but it does not prevent a user from introducing new code changes. Firewalls on the software development servers protect the servers from external attacks, but they do not prevent a user from accessing the servers internally. Longer and more complex password requirements make it harder for attackers to guess or crack passwords, but they do not prevent a user from using their own valid credentials.
References
1: Role-Based Access Control (RBAC) - Definition and Examples 2: Network+ (Plus) Certification | CompTIA IT Certifications
3: [What is the Principle of Least Privilege? - Definition from Techopedia]
NEW QUESTION 13
A technician is installing multiple UPS units in a major retail store. The technician is required to keep track of all changes to new and old equipment. Which of the following will allow the technician to record these changes?
- A. Asset tags
- B. A smart locker
- C. An access control vestibule
- D. A camera
Answer: A
Explanation:
Asset tags will allow the technician to record changes to new and old equipment when installing multiple UPS units in a major retail store. Asset tags are labels or stickers that are attached to physical assets such as computers, printers, servers, or UPS units. They usually contain information such as asset name, serial number, barcode, QR code, or RFID chip that can be scanned or read by an asset management system or software. Asset tags help track inventory, location, status, maintenance, and ownership of assets. References: https://www.camcode.com/asset-tags/asset-tagging-guide/
NEW QUESTION 14
Which of the following is MOST likely to generate significant East-West traffic in a datacenter?
- A. A backup of a large video presentation to cloud storage for archival purposes
- B. A duplication of a hosted virtual server to another physical server for redundancy
- C. A download of navigation data to a portable device for offline access
- D. A query from an IoT device to a cloud-hosted server for a firmware update
Answer: B
Explanation:
East-West traffic refers to data flows between servers or devices within the same datacenter. When a hosted virtual server is duplicated to another physical server for redundancy, it generates significant East-West traffic as the data is replicated between the two servers. References:
✑ Network+ N10-008 Objectives: 3.3 Given a scenario, implement secure network architecture concepts.
NEW QUESTION 15
A company streams video to multiple devices across a campus. When this happens, several users report a degradation of network performance. Which of the following would MOST likely address this issue?
- A. Enable IGMP snooping on the switches.
- B. Implement another DHCP server.
- C. Reconfigure port tagging for the video traffic.
- D. Change the SSID of the APs
Answer: A
NEW QUESTION 16
A network administrator needs to monitor traffic on a specific port on a switch. Which of the following should the administrator configure to accomplish the task?
- A. Port security
- B. Port tagging
- C. Port mirroring
- D. Media access control
Answer: C
Explanation:
Port mirroring is a technique that allows a network administrator to monitor the traffic on a specific port on a switch by sending a copy of the packets seen on that port to another port where a monitoring device is connected1. Port mirroring can be used to analyze and debug data, diagnose errors, or perform security audits on the network without affecting the normal operation of the switch
NEW QUESTION 17
A technician is investigating a SAN switch that has a high number of CRC errors. Which of the following is the MOST likely cause of the errors?
- A. Break in the fiber
- B. Bad switch port
- C. Mismatched duplex
- D. Memory errors
Answer: B
Explanation:
A bad switch port is the most likely cause of CRC errors on a SAN switch. CRC stands for cyclic redundancy check, which is a method of detecting errors in data transmission. A SAN switch is a device that connects storage devices and servers in a storage area network (SAN), which is a high-performance network that provides block-level access to data. A bad switch port can cause CRC errors due to physical damage, faulty wiring, or misconfiguration. CRC errors can result in data corruption or loss, which can affect the performance and availability of the SAN. References: [CompTIA Network+ Certification Exam Objectives], What are CRC Errors and How Do I Fix Them? | ITIGIC
NEW QUESTION 18
A Chief Information Officer (CIO) wants to improve the availability of a company's SQL database Which of the following technologies should be utilized to achieve maximum availability?
- A. Clustering
- B. Port aggregation
- C. NIC teaming
- D. Snapshots
Answer: A
Explanation:
Clustering is a technique that involves grouping multiple servers or instances together to provide high availability and fault tolerance for a database. Clustering can help improve the availability of a SQL database by allowing automatic failover and load balancing between the cluster nodes. If one node fails or becomes overloaded, another node can take over the database operations without disrupting the service. References: https://www.educba.com/sql-cluster/
NEW QUESTION 19
Which of the following is the physical security mechanism that would MOST likely be used to enter a secure site?
- A. A landing page
- B. An access control vestibule
- C. A smart locker
- D. A firewall
Answer: B
Explanation:
An access control vestibule is a physical security mechanism that consists of a small room or chamber with two doors, one leading to the outside and one leading to the secure site. The doors are controlled by an electronic system that verifies the identity and authorization of the person entering before allowing access to the next door. A landing page is a web page that appears when a user clicks on a link or advertisement. A smart locker is a physical security mechanism that allows users to store and retrieve items using a code or biometric authentication. A firewall is a network security device that monitors and filters incoming and outgoing traffic based on predefined rules. References: [CompTIA Network+ Certification Exam Objectives], Domain 4.0 Network Operations, Objective 4.1: Explain the importance of documentation and diagrams, Subobjective: Physical security devices (locks, cameras, etc.)
NEW QUESTION 20
A technician is connecting multiple switches to create a large network for a new office. The switches are unmanaged Layer 2 switches with multiple connections between each pair. The network is experiencing an extreme amount of latency. Which of the following is MOST likely occurring?
- A. Ethernet collisions
- B. A DDoS attack
- C. A broadcast storm
- D. Routing loops
Answer: C
Explanation:
A broadcast storm is most likely occurring when connecting multiple unmanaged Layer 2 switches with multiple connections between each pair. A broadcast storm is a situation where broadcast packets flood a network segment and consume all the available bandwidth. It can be caused by loops in the network topology, where broadcast packets are endlessly forwarded by switches without any loop prevention mechanism. Unmanaged switches do not support features such as Spanning Tree Protocol (STP) or Rapid Spanning Tree Protocol (RSTP) that can detect and block loops. References: https://www.cisco.com/c/en/us/support/docs/lan-switching/spanning-tree-protocol/10556- 16.html
NEW QUESTION 21
......
100% Valid and Newest Version N10-009 Questions & Answers shared by Certshared, Get Full Dumps HERE: https://www.certshared.com/exam/N10-009/ (New 179 Q&As)